Kaspersky Lab uncovers Windows zero-day exploited by recently discovered threat actor13 March 2019Kaspersky Lab’s automated technologies have detected a new exploited vulnerability in Microsoft Windows, believed to have been used in targeted attacks by at least two threat actors, including the recently discovered SandCat. This is the fourth zero-day exploit to be discovered in the wild by Kaspersky Lab’s Automatic Exploit Prevention technology. Kaspersky Lab reported the vulnerability, allocated CVE-2019-0797 to Microsoft, which has released a patch. Zero-day vulnerabilities are previously unknown software bugs that can be exploited by attackers to breach a victim’s device and network. The new exploit uses a vulnerability in Microsoft Windows’ graphic subsystem to achieve local privilege escalation. This provides the attacker with full control over a victim’s computer. The malware sample examined by Kaspersky Lab researchers shows that the exploit targets OS versions Windows 8 to Windows 10. The researchers believe the detected exploit could have be used by several threat actors including, but possibly not limited to, FruityArmor and SandCat. FruityArmor is known to have used zero-days in the past, while SandCat is a new threat actor discovered only recently. “The discovery of a new Windows zero-day being actively exploited in the wild shows that such expensive and rare tools remain of great interest to threat actors, and organizations need security solutions that can protect against such unknown threats. It also reaffirms the importance of collaboration between the security industry and software developers: bug hunting, responsible disclosure and prompt patching are the best ways of keeping users safe from new and emerging threats,” – said Anton Ivanov, a security expert at Kaspersky Lab. 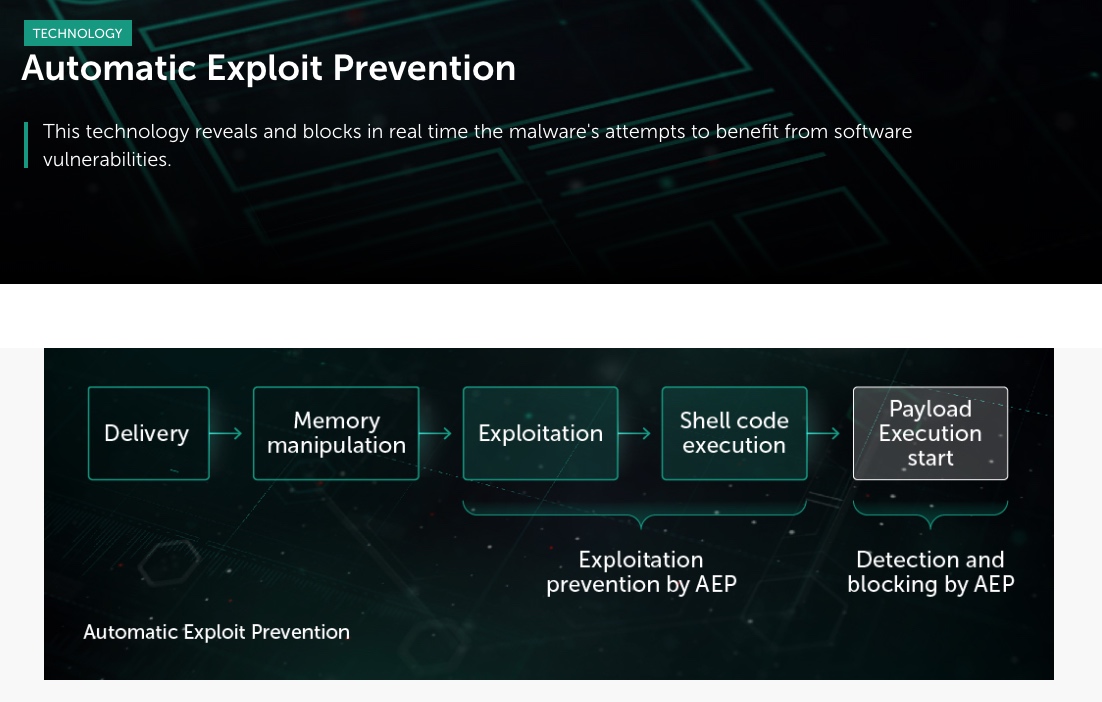 The exploited vulnerability was detected by Kaspersky Lab’s Automatic Exploit Prevention technology, embedded in most of the company’s products. Kaspersky Lab products detect the exploit as:
Kaspersky Lab recommends taking the following security measures:
For further details on the new exploit see the report on Securelist. To take a closer look at the technologies that detected this and other zero-days in Microsoft Windows, a recorded Kaspersky Lab webinar is available to view on demand. |